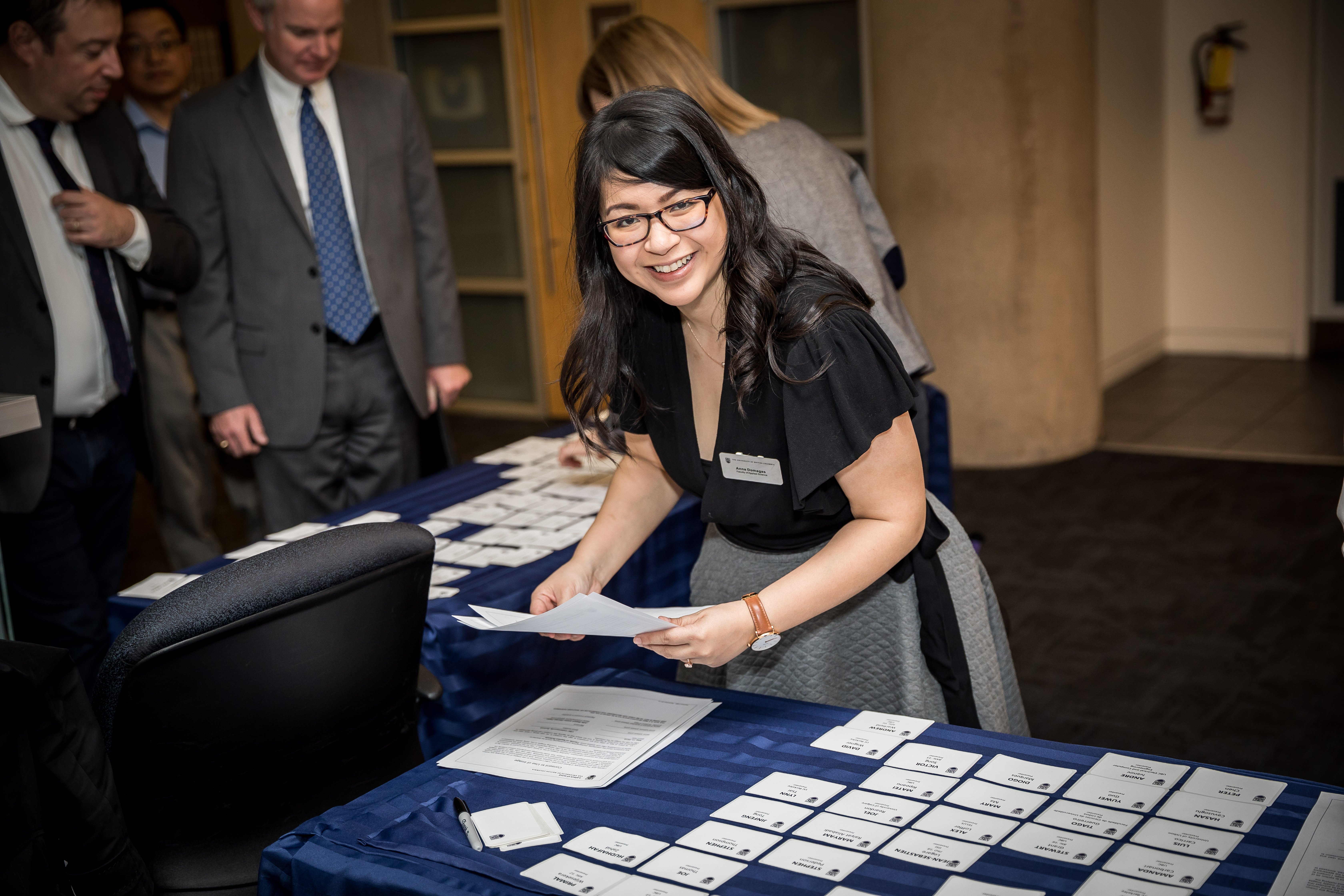
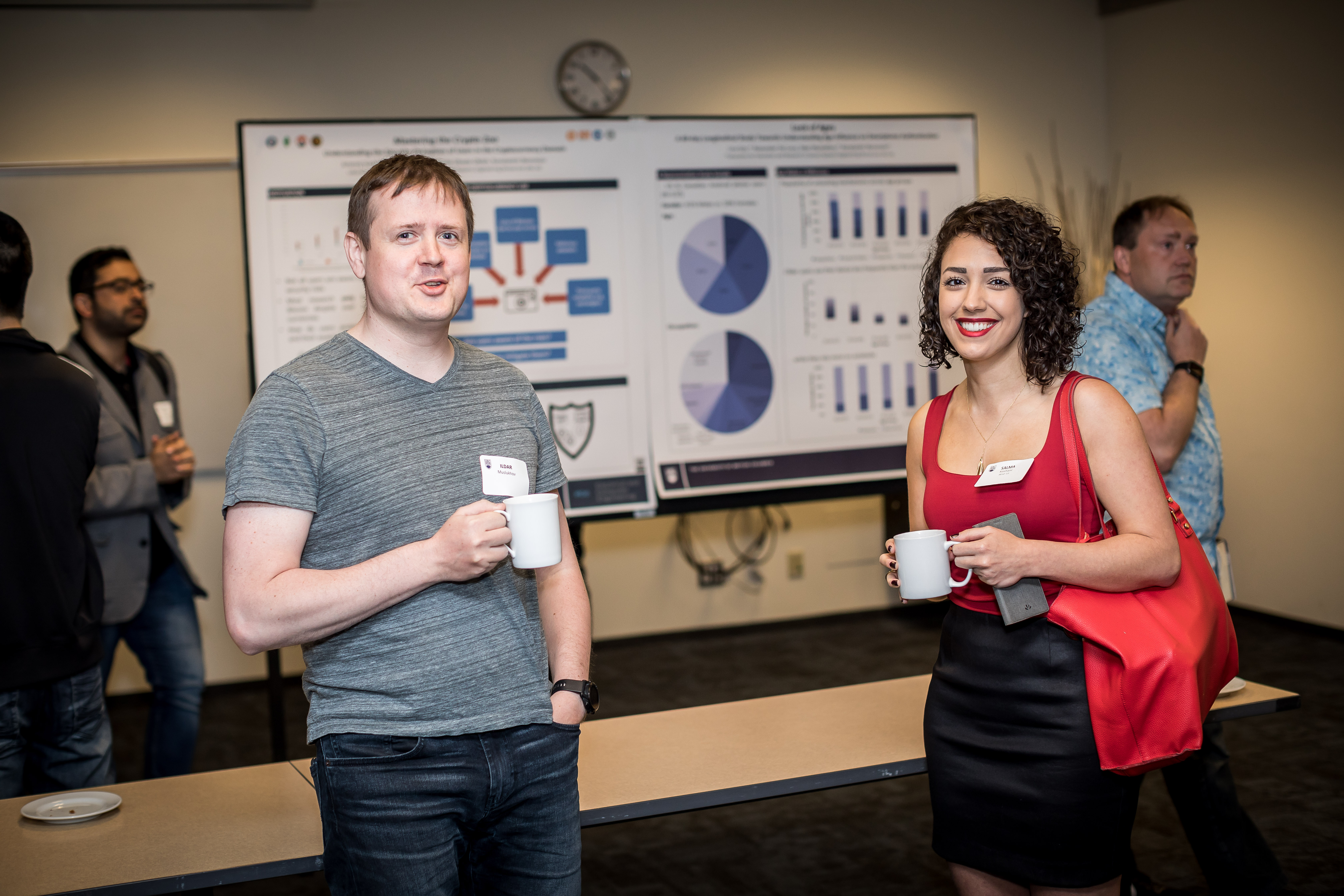
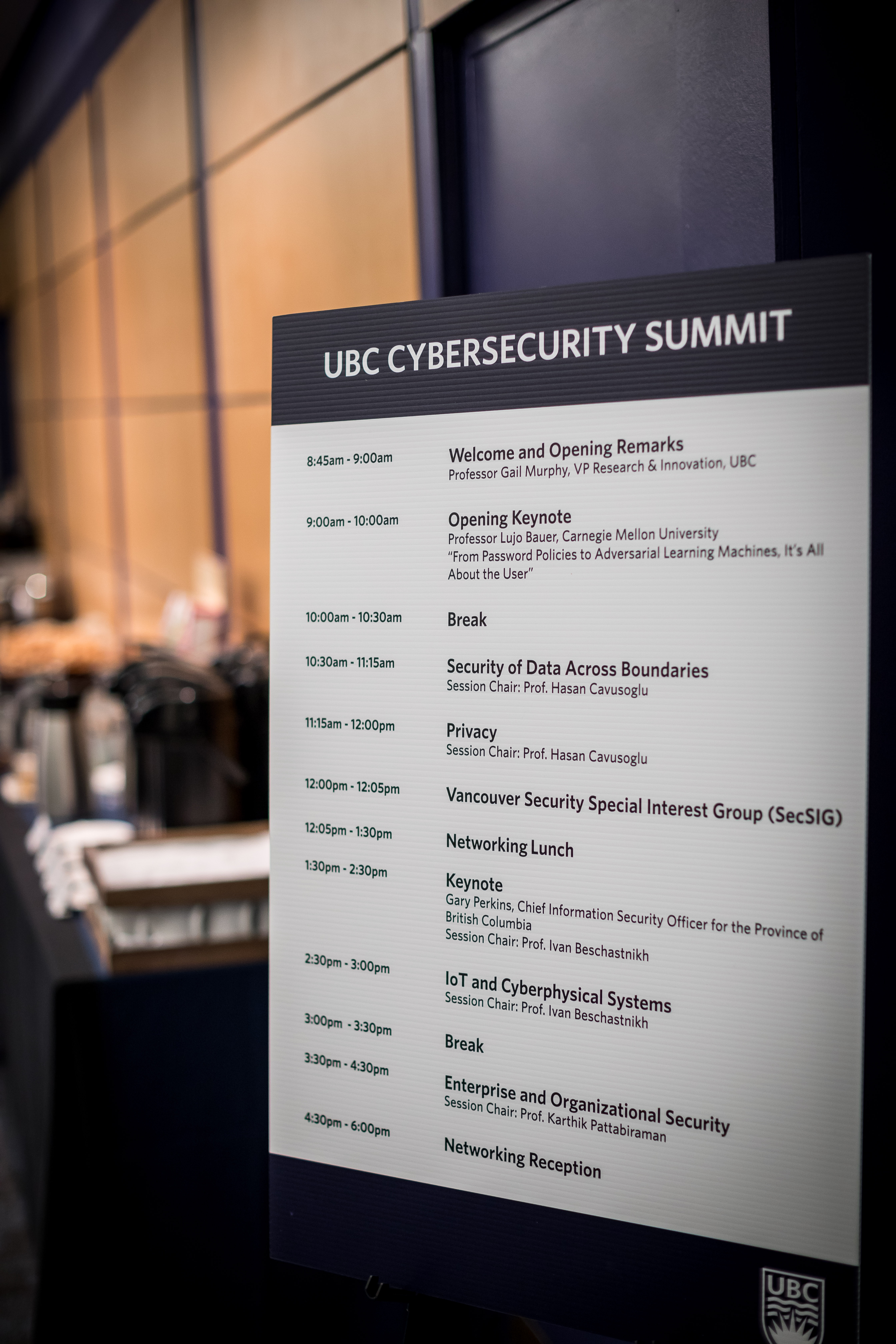
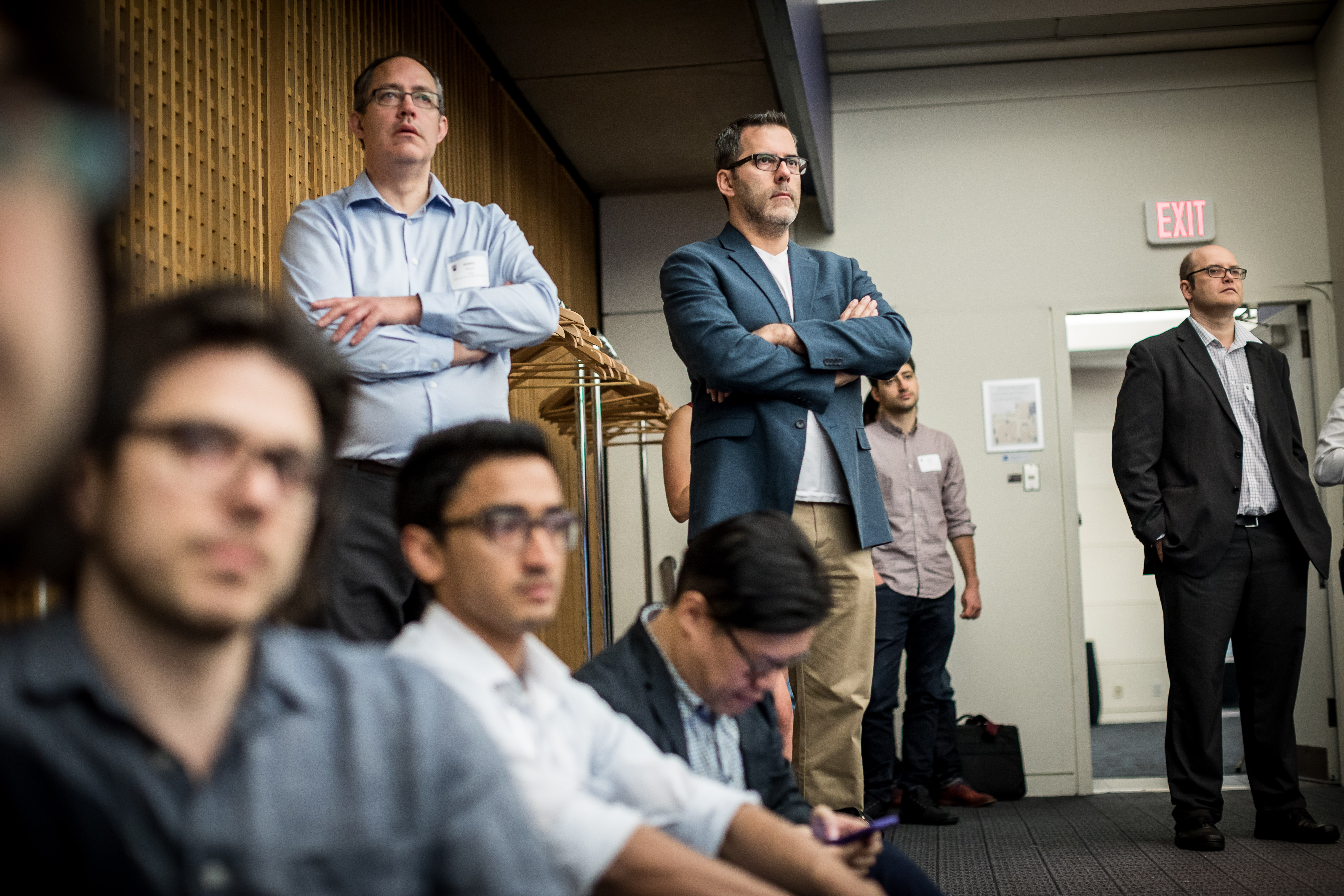
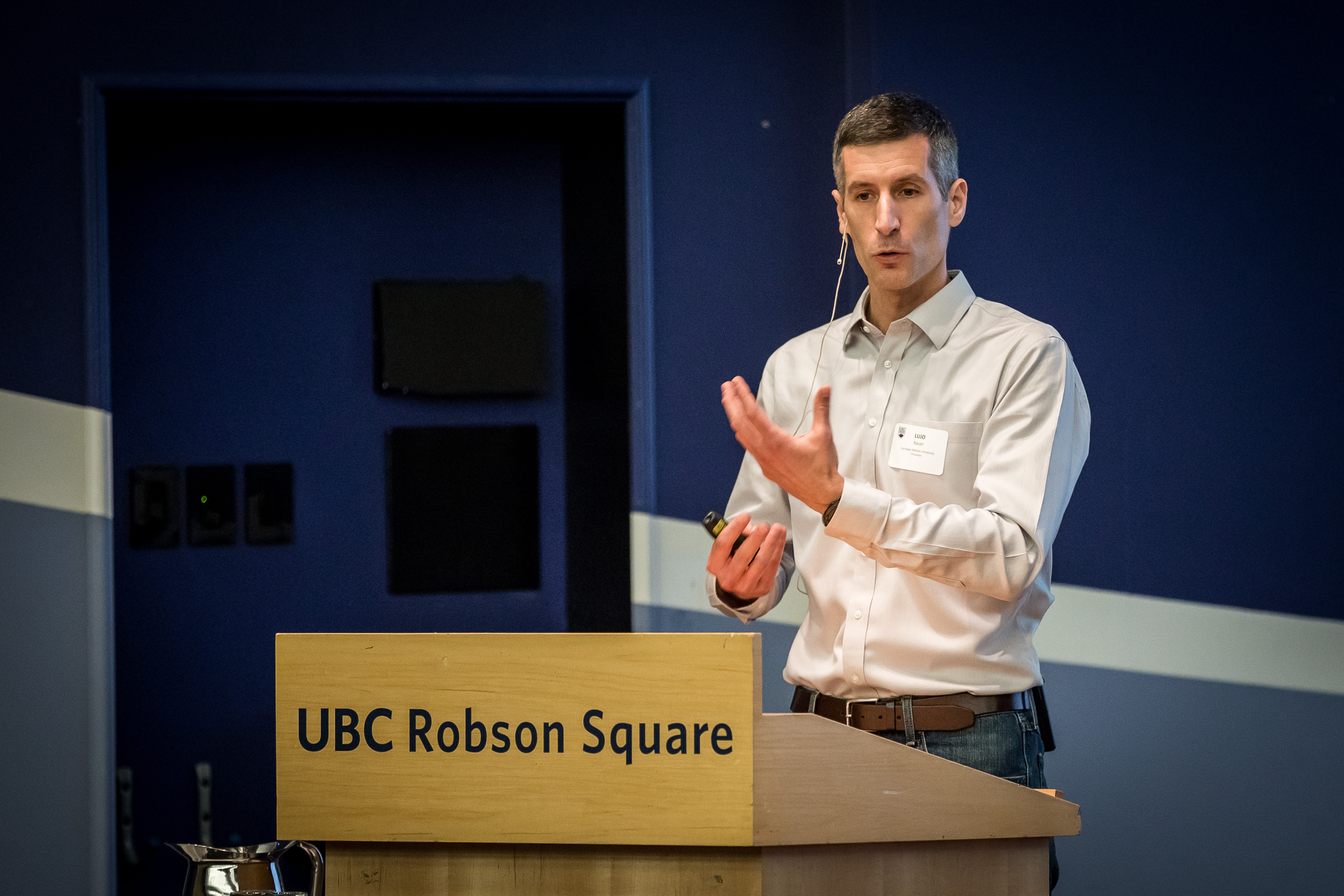
UBC Cybersecurity Summit was held on May 11, 2018, at UBC Robson Square, in Vancouver Downtown. It showcased research by UBC faculty and graduate students in Cybersecurity.
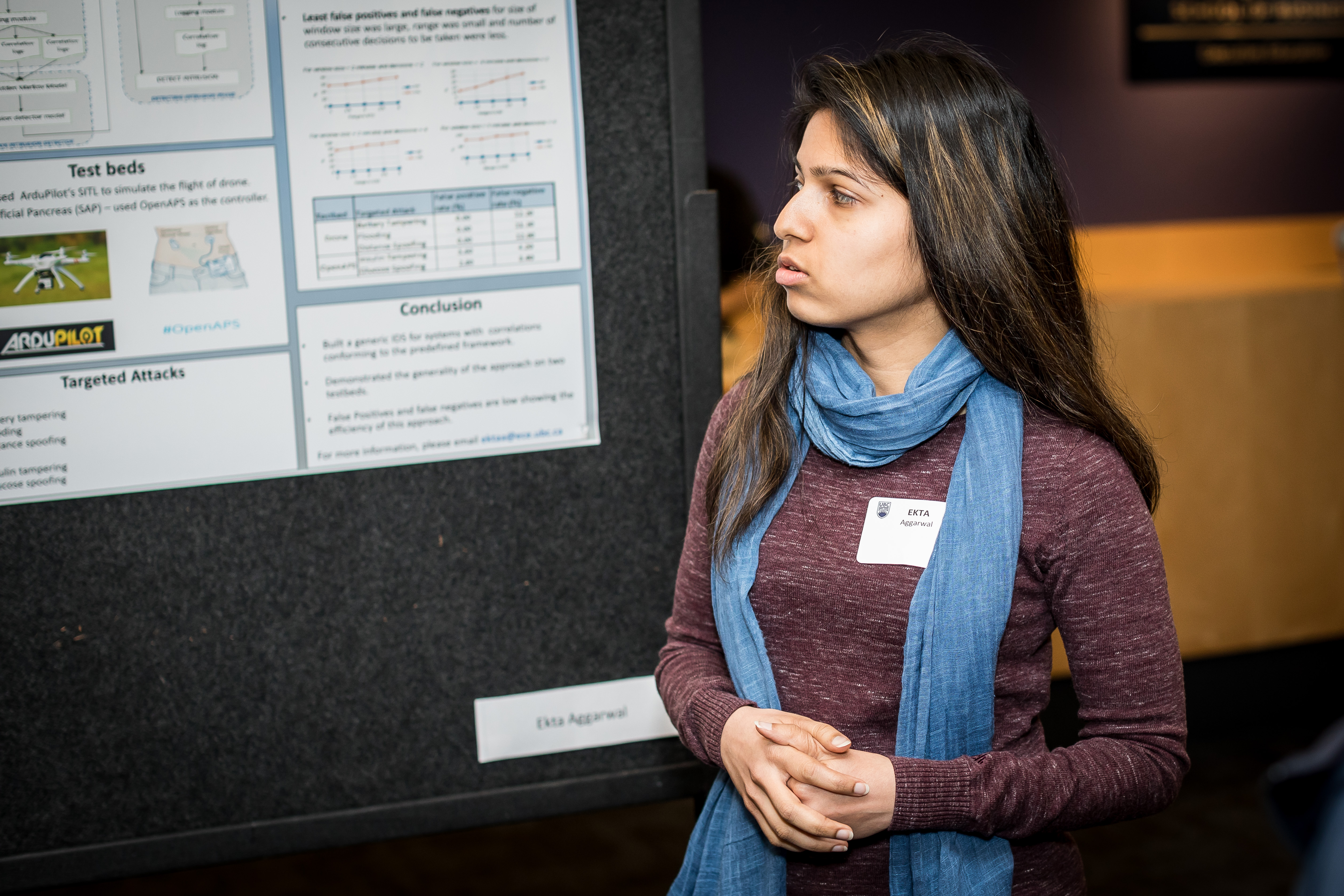
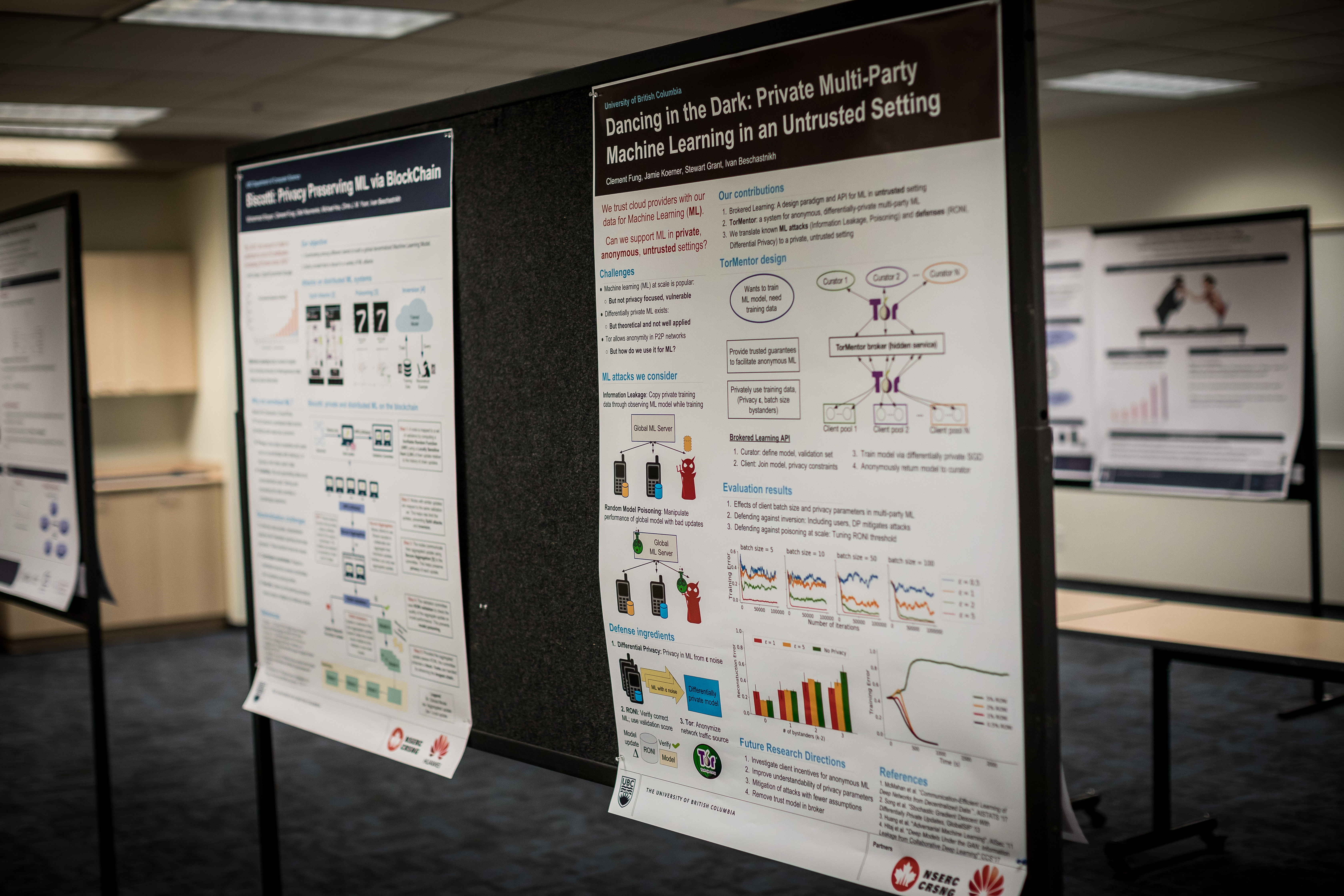
It was a full day event, with outstanding keynotes by BC CISO Gary Perkins and CMU Prof. Lujo Bauer, 12 project presentations by PhD and Masters students, and 20+ posters on recent and ongoing research at UBC. The summit attracted 177 participants from 55 organizations. The summit was collocated with a meeting of the Vancouver Security Special Interest Group.
Most of the summit presentations can be watched below
View pictures from the summit